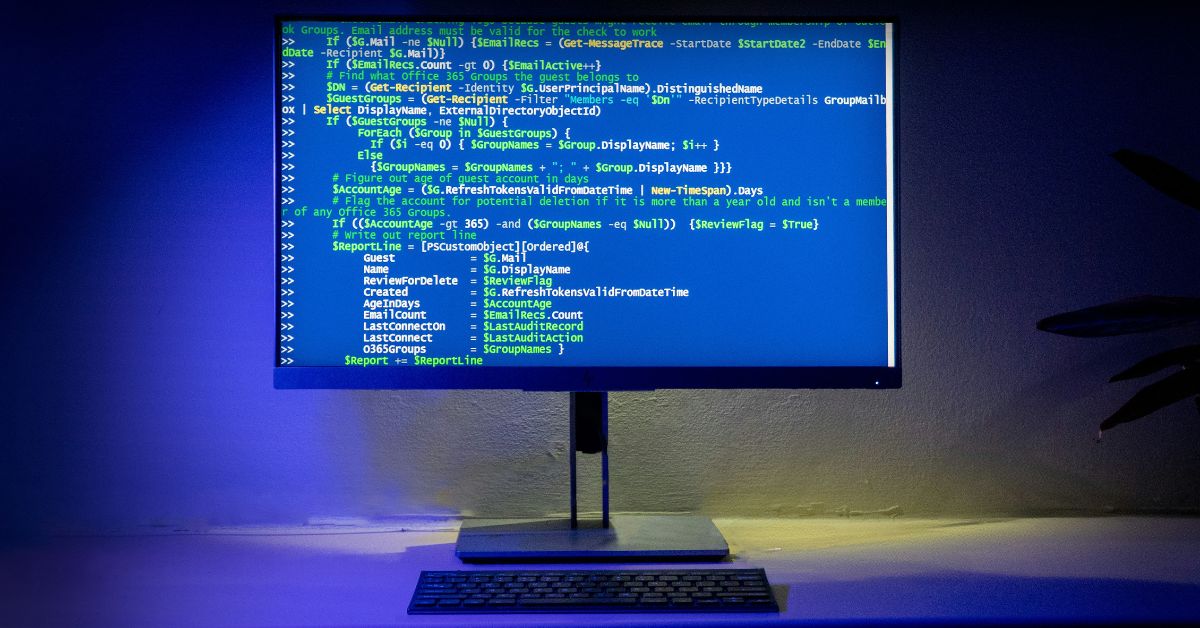
Cybersecurity as a National Defense Strategy
Cybersecurity is a core component of modern national defense, serving as both a shield to protect a nation’s critical infrastructure and a sword to project power and conduct espionage in the new, fifth domain of warfare: cyberspace. As of September 2, 2025, for a nation like Pakistan, a strong national cybersecurity strategy is as essential…