The Rise of Cyber Warfare Between Nations
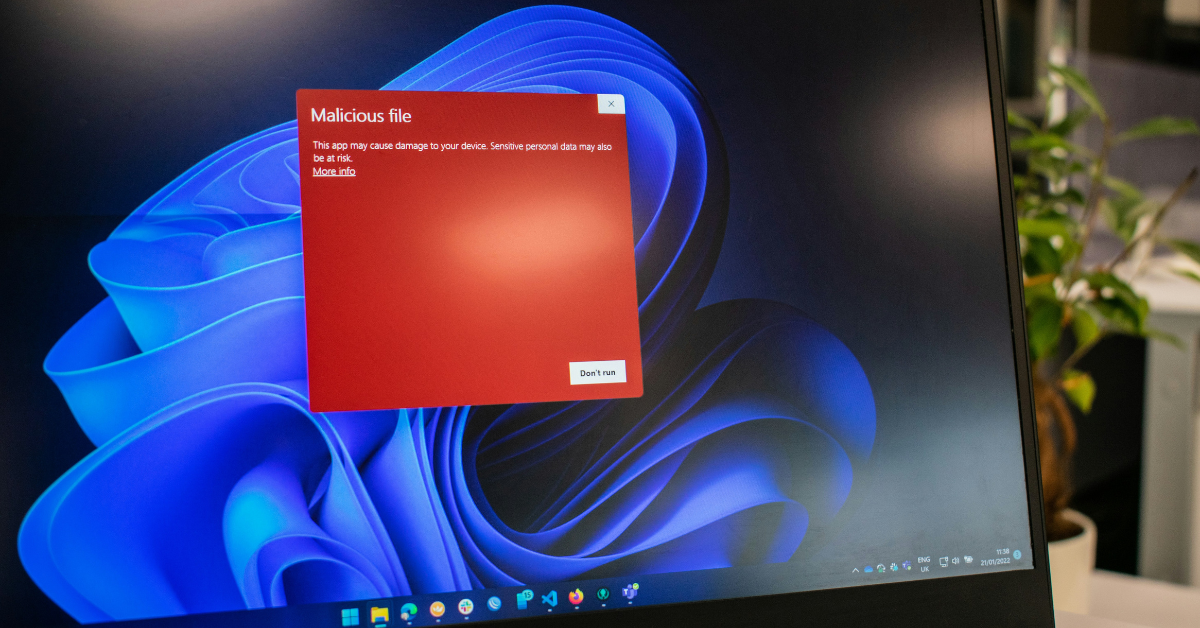
The rise of cyber warfare represents a fundamental shift in the nature of international conflict. As of August 28, 2025, cyberspace has been firmly established as the “fifth domain” of warfare, alongside land, sea, air, and space. For nations around the world, including Pakistan, the digital realm is no longer just a space for communication…