Cybersecurity for the Next Billion Internet Users
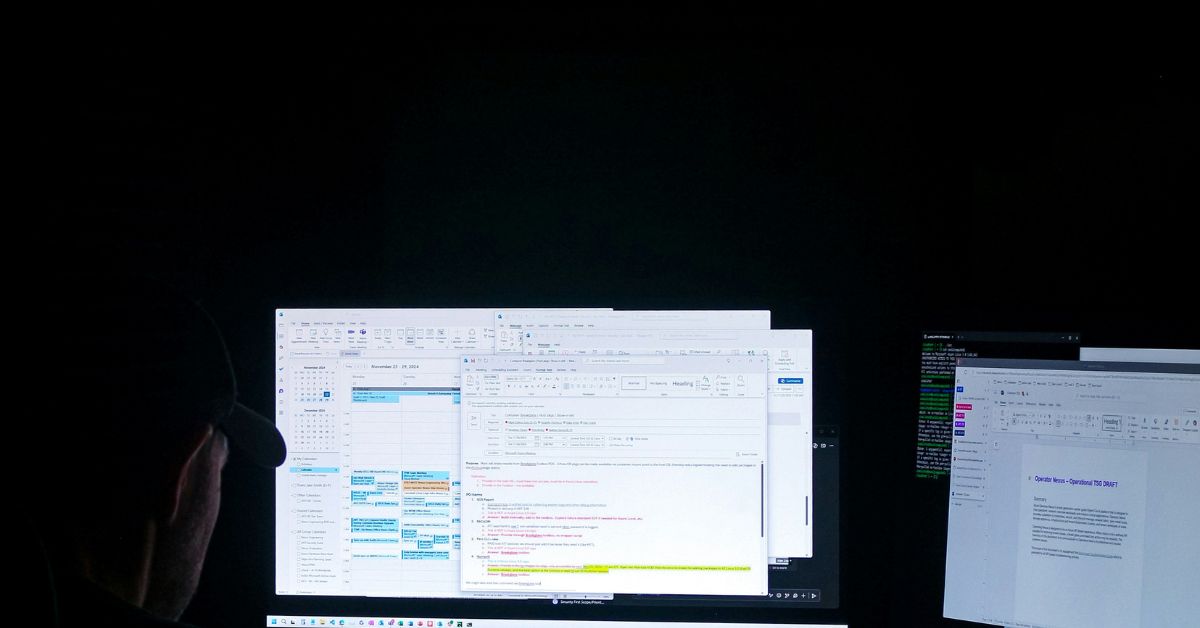
The primary cybersecurity challenge for the next billion internet users is their vulnerability to common scams and fraud due to a lack of digital literacy, compounded by their reliance on low-cost, often less secure mobile devices. The solution requires a collaborative effort focused on simplified, accessible education, and building security and trust directly into the…